What Is a Crypto Wallet, Really? Types, Tradeoffs, and How to Choose
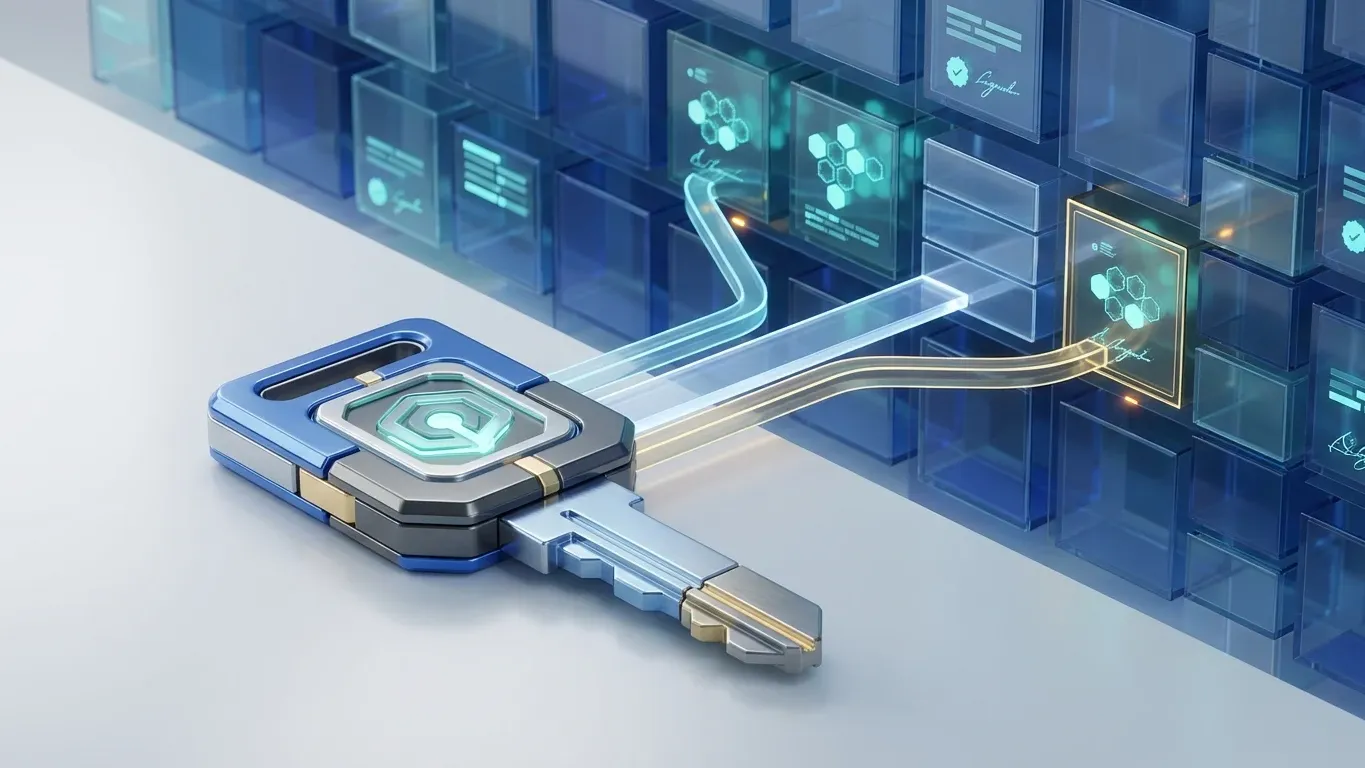
Your crypto lives on the blockchain. Your wallet holds the keys that prove it is yours. Here is how that actually works, what types exist, and how to pick the right one.
Key Takeaways
- A crypto wallet stores your private keys, not your cryptocurrency. Your crypto exists on the blockchain, and the wallet holds the credentials that prove ownership and authorize transactions.
- The two primary categories are hot wallets (connected to the internet, convenient for frequent use) and cold wallets (offline, more secure for long-term storage).
- Custodial wallets let a third party manage your keys on your behalf. Non-custodial wallets give you full control and full responsibility, including the risk of permanent loss.
- Choosing the right wallet depends on how often you transact, how much you hold, your technical comfort level, and whether you need access to DeFi or dApps.
- An estimated 2.3 to 3.7 million Bitcoin is permanently inaccessible due to lost private keys and seed phrases, making wallet security one of the most consequential decisions in crypto.
What a Crypto Wallet Actually Is (And What It Is Not)
A crypto wallet is a software application or hardware device that stores the cryptographic keys (public and private) needed to send, receive, and manage cryptocurrency on a blockchain, and despite what the name suggests, it does not hold your coins or tokens. At Blockready, we structure Module 6 (Wallets and Security) around exactly this foundational distinction, because getting the mental model wrong at the start creates confusion that compounds with every new concept you encounter.
The most common misunderstanding new users have about crypto wallets is the name itself. In everyday life, a wallet holds cash. A crypto wallet holds keys. The difference matters because it changes how you think about security, backup, and recovery.
Think of it this way: your cryptocurrency is a record on a public ledger (the blockchain). That record says "this address controls X amount of Bitcoin." Your wallet holds the private key that proves you own that address. Without the key, you cannot move the funds. With the key, anyone can. The wallet is closer to a keychain than a purse.
This distinction also explains why you can access the same crypto from multiple devices. If you restore your wallet on a new phone using your seed phrase, your funds are not "transferred" from the old device. The new device simply gains the ability to sign transactions for the same blockchain address. The crypto never moved. Only your access point changed.
How Crypto Wallets Work Under the Hood
Public keys, private keys, and addresses
Every crypto wallet operates on a pair of cryptographic keys generated together through a mathematical process. The private key is a long, randomized string of characters that functions as your proof of ownership. It must remain secret. The public key is derived from the private key and can be shared freely. Your wallet address, the string you give someone so they can send you crypto, is a compressed version of your public key.
The relationship between these keys is one-directional. You can always derive the public key from the private key, but you cannot reverse-engineer the private key from the public key. This asymmetric design is what makes blockchain technology secure without requiring a central authority to verify identity.
What happens when you send crypto
Sending cryptocurrency involves more steps than most users realize. When you tap "send" in a wallet app, the software is executing a series of cryptographic operations in the background.
HOW A CRYPTO TRANSACTION MOVES FROM YOUR WALLET TO THE BLOCKCHAIN
Source: Adapted from Bitcoin and Ethereum protocol documentation
The critical thing to notice is that your private key never leaves your device during this process. The wallet uses it to create a digital signature, and only the signature is shared with the network. This is why private key security is the foundation of everything else in crypto. If someone obtains your private key, they can sign transactions on your behalf, and the network will treat those transactions as legitimate.
Seed phrases and recovery
When you set up a new wallet, it generates a seed phrase (also called a recovery phrase), typically a list of 12 or 24 randomly selected words from a standardized dictionary. This seed phrase is a human-readable backup of your private key. From those words, the wallet can regenerate your private key and all associated addresses.
The relationship matters: the seed phrase is the master key. The private key is derived from it. If your phone breaks or your hardware wallet is damaged, the seed phrase is the only path to recovering access. No password reset, no customer service line, no "forgot my key" button. This is not a flaw. It is how decentralized ownership works by design.
Types of Crypto Wallets
Crypto wallets can be categorized along two independent axes: connectivity (hot vs. cold) and custody (who holds the keys). Most confusion comes from treating these as a single spectrum when they are actually two separate decisions.
Hot wallets vs. cold wallets
A hot wallet is any wallet connected to the internet. This includes mobile apps, browser extensions, and desktop software. Hot wallets are convenient for frequent transactions, but their internet connection creates a larger attack surface for malware, phishing, and remote exploits.
A cold wallet stores your private keys in an environment that is never connected to the internet by default. Hardware wallets and paper wallets fall into this category. Cold wallets reduce exposure to online threats, but they are less convenient for everyday use.
Custodial vs. non-custodial: who holds the keys?
This is the more consequential distinction, and the one most beginners overlook. A custodial wallet means a third party (usually a crypto exchange) holds your private keys on your behalf. You access your funds through their platform. If the exchange gets hacked or goes bankrupt, your funds may be at risk.
A non-custodial wallet means you hold your own private keys. No third party can freeze your account, censor your transactions, or access your funds. But if you lose your seed phrase, no one can help you recover access.
Ledger analysts estimate that between 2.3 and 3.7 million Bitcoin are permanently inaccessible as of early 2025, largely due to lost private keys and seed phrases. That figure represents tens of billions of dollars in value that no technology can recover. Understanding the custody model before you transfer any significant amount is the single most important security decision you will make in crypto.
TYPES OF CRYPTOCURRENCY WALLETS
Source: Blockready Module 6 (Wallets and Security)
Hardware wallets
Hardware wallets are physical devices (typically resembling USB drives) that generate and store your private keys in a secure, offline environment. When you want to send crypto, the hardware wallet signs the transaction internally and sends only the signed output to your connected device. Your private key never leaves the hardware.
This air-gapped approach makes hardware wallets the most resistant to remote attacks. Even if the computer you connect the device to is compromised, the private key remains protected inside the device. The tradeoff is cost ($50 to $200), the inconvenience of needing the physical device for every transaction, and the risk of physical loss.
Software and mobile wallets
Software wallets are free applications you install on your phone or computer. They generate your keys on the device and allow direct interaction with blockchain networks. Browser-extension wallets like MetaMask are particularly popular because they connect directly to decentralized applications and DeFi protocols.
Software wallets are the most common entry point for new users because they are free, fast to set up, and support a wide range of tokens. The security limitation is that your keys exist on a device connected to the internet.
Paper wallets (and why they are mostly obsolete)
A paper wallet is a printed copy of your private key and public address. Completely offline, immune to digital attacks. But paper wallets are fragile, easily damaged, and difficult to use for transactions. Most security professionals now recommend hardware wallets instead.
Smart contract wallets: the emerging category
A newer class of wallets runs on smart contract code deployed directly to the blockchain. These wallets, enabled by the ERC-4337 standard launched in March 2023, add capabilities traditional wallets cannot offer: social recovery, gasless transactions, multi-signature requirements, and programmable spending limits.
Over 40 million smart contract accounts have been deployed across Ethereum and Layer 2 networks since 2023, according to Alchemy's account abstraction data. The May 2025 Pectra upgrade introduced EIP-7702, which allows traditional wallets to temporarily gain smart contract wallet features without requiring migration. This directly addresses the seed phrase loss problem that has locked billions of dollars in inaccessible wallets.
How to Choose the Right Wallet
Choosing a wallet is not about finding the "best" one. It is about matching the right tool to your specific situation. Here is a mistake that catches many new users: they pick a wallet based on brand recognition or a friend's recommendation without understanding whether they need custodial or non-custodial, hot or cold. Blockready's Module 6 covers wallet selection across 10 dedicated lessons, including custodial vs. non-custodial tradeoffs, seed phrase management strategies, and hardware wallet setup procedures.
WALLET SELECTION: MATCHING YOUR NEEDS TO THE RIGHT TYPE
Source: Blockready Module 6 (Wallets and Security)
A few practical guidelines based on common situations:
If you are buying crypto for the first time and holding less than $500, a custodial exchange wallet is a reasonable starting point. The priority at this stage is learning how transactions work without the added complexity of managing your own keys.
If you are holding amounts you would be uncomfortable losing, move to a non-custodial software wallet and properly secure your seed phrase.
If you are holding amounts that represent a meaningful portion of your savings, a hardware wallet is the standard recommendation. The $50 to $200 cost is negligible compared to the value it protects.
Many experienced users combine approaches: a custodial exchange account for active trading, a software wallet for DeFi interaction, and a hardware wallet for long-term storage.
Common Wallet Mistakes and How to Avoid Them
One of the most common mistakes new crypto users make is treating a wallet address like a bank account number, something you can recover if you lose access. It is not. If you lose your seed phrase, no customer support team can help you. Understanding this before you transfer any funds is exactly the kind of foundational knowledge that separates confident participants from anxious ones.
Beyond seed phrase handling, several other mistakes cause preventable losses. Sending crypto to the wrong blockchain (for example, sending Ethereum tokens to a Bitcoin address) can result in permanently lost funds. Always verify the network before sending. When sending to a new address for the first time, send a small test transaction first.
Connecting your primary wallet to unfamiliar websites or dApps creates exposure to malicious smart contracts that can drain your holdings. Many experienced users maintain a separate "hot" wallet with minimal funds specifically for interacting with new protocols. The 2026 crypto scams guide covers how approval phishing exploits this exact vulnerability. For a deeper look at how attack vectors have evolved, the Blockready wallet security guide covers the full history.
Frequently Asked Questions
Go Deeper on Wallet Security With Structure
Blockready's masterclass covers wallets, key management, and security across 13 modules and 150+ lessons. From custodial tradeoffs to hardware wallet setup. Built for clarity, not hype.
Explore the Full Course