The Bybit Hack Explained: How $1.5 Billion Was Stolen and Where It Went
The largest crypto theft in history was not a brute-force break-in. It was a supply chain compromise that fooled the people holding the keys.
Key Takeaways
- The Bybit hack ($1.5 billion in ETH, February 2025) exploited a third-party wallet provider's software, not the blockchain itself.
- North Korea's Lazarus Group executed the attack, and the FBI confirmed attribution within five days.
- Most stolen funds were converted to Bitcoin through decentralized exchanges and cross-chain bridges, with roughly 28% going untraceable within two months.
- Multisig wallets failed here not because of a cryptographic flaw, but because the signing interface was compromised.
- Understanding how attacks and laundering actually work provides better protection than memorizing a security checklist.
What Happened at Bybit
The Bybit hack was a supply chain attack on February 21, 2025, in which hackers drained approximately 401,000 ETH (worth roughly $1.5 billion) from one of the exchange's cold wallets by compromising the third-party signing interface rather than the blockchain or multisig cryptography itself. At Blockready, we use this incident as a case study in Module 6 (Wallets) because it demonstrates a principle that applies to everyone holding crypto: your security is only as strong as the weakest link in your entire software stack.
The attack took place during what appeared to be a routine transfer from cold storage to a warm wallet, a standard operation that exchanges perform regularly to keep trading operations funded.
Within minutes, the funds were gone. Within hours, the stolen ETH was already being split across dozens of wallets. Within five days, the FBI publicly attributed the attack to North Korea's Lazarus Group (also tracked under the name "TraderTraitor"), a state-backed hacking operation responsible for billions of dollars in crypto theft since 2017.
THE BYBIT HACK BY THE NUMBERS (FEBRUARY 2025)
Sources: Bybit, FBI, Elliptic
This was not just the largest crypto hack ever recorded. According to blockchain analytics firm Elliptic, it was likely the largest single theft of any kind in history, surpassing even the $1 billion Saddam Hussein took from the Iraqi Central Bank in 2003.
Bybit's CEO, Ben Zhou, addressed users within 30 minutes of the breach. The exchange kept withdrawals open throughout the crisis and restored 1:1 reserve backing within 72 hours through a combination of emergency loans from Galaxy Digital, FalconX, and Wintermute, plus a proof-of-reserves audit by cybersecurity firm Hacken. No customer funds were lost from the exchange's balance sheet.
But the stolen $1.5 billion? That is a very different story.
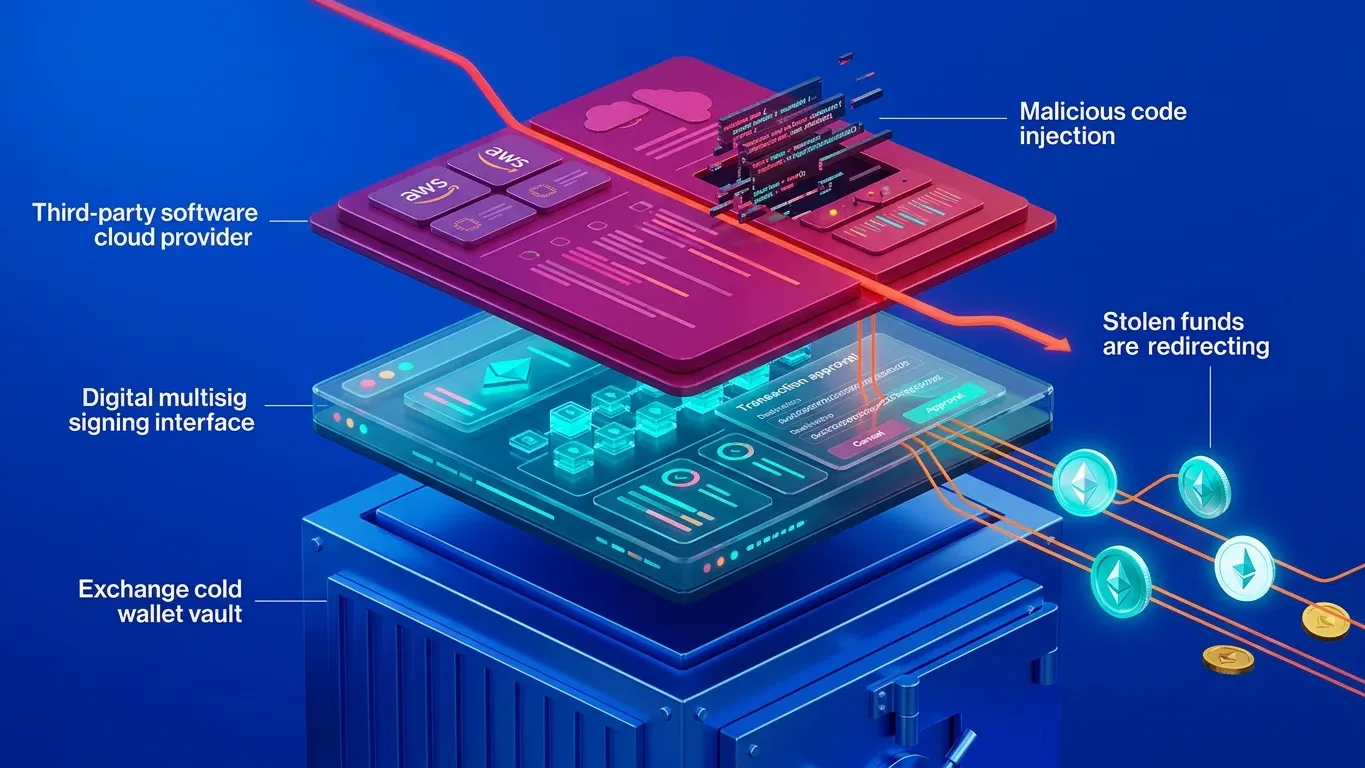
How the Attack Actually Worked
This is where most coverage of the Bybit hack gets either too technical or too vague. Here is what actually happened.
Bybit used Safe{Wallet}, a widely adopted multi-signature wallet platform, to manage its cold storage. Multi-signature (multisig) means multiple people must approve a transaction before it goes through. In Bybit's case, at least three signers were required. This is considered one of the strongest security setups for crypto wallets.
The attackers did not break the multisig cryptography. They did not guess anyone's private key. They went after the software that shows signers what they are approving. That distinction matters.
ANATOMY OF A SUPPLY CHAIN ATTACK: THE BYBIT HACK IN 4 STEPS
Sources: Sygnia forensic investigation, NCC Group technical analysis, Mandiant preliminary report (via Safe{Wallet})
This type of attack is called a supply chain compromise. The target (Bybit) was not attacked directly. Instead, the attackers went after a trusted third-party tool that Bybit depended on. It is the same principle behind some of the most damaging cyberattacks in recent years, across both crypto and traditional industries. And it reveals a critical blind spot: your security is only as strong as the weakest link in your entire software stack.
Where the Money Went
Understanding how $1.5 billion in stolen crypto gets laundered is genuinely educational. Not in a "how to do it" sense. In a "how blockchain transparency works in practice, and where it breaks down" sense. The laundering process followed a pattern that blockchain investigators recognize from previous Lazarus Group operations, but at a scale that overwhelmed existing tracking capacity.
Step 1: Swap Stolen Tokens for Native Assets
In the minutes after the theft, the attackers converted stolen tokens (like stETH and cmETH) into plain ETH using decentralized exchanges. Why? Because tokens issued by specific projects can sometimes be frozen by their issuers. A company that controls a token contract can blacklist a wallet address, effectively locking the stolen assets in place. ETH, as a native blockchain asset, has no issuer and cannot be frozen by anyone. This first step was about removing that risk.
Step 2: Split, Scatter, and Bridge
The stolen ETH was distributed across 50 wallets, each holding roughly 10,000 ETH. Over the following nine days, these wallets were emptied one by one. The majority of the ETH was then moved through THORChain, a decentralized cross-chain liquidity protocol, and converted into Bitcoin. By March 2025, Bybit CEO Ben Zhou confirmed that 86% of the stolen ETH had been converted to BTC and distributed across more than 35,000 wallets.
Why Bitcoin? Because Bitcoin's UTXO transaction model works like physical cash, where each individual "bill" must be traced separately. Ethereum's account-based model functions more like a bank account with a running balance, making fund flows easier to follow. Converting to Bitcoin made the forensic job significantly harder.
Step 3: Mixing and Cash-Out
Once in Bitcoin, the funds were fed through mixing services (including Wasabi Wallet and CryptoMixer) designed to break the connection between sender and receiver. From mixers, funds typically flow to over-the-counter (OTC) trading desks, suspected largely in China according to Elliptic's analysis, where they can be exchanged for fiat currency.
Some services facilitated this process willingly. The eXch exchange processed tens of millions in stolen funds and refused to block the activity despite direct requests from Bybit. THORChain generated $5.5 million in transaction fees from the laundering volume. This highlights an uncomfortable reality: the decentralized infrastructure that provides freedom from gatekeepers also provides freedom for criminals. That is not an argument against decentralization. But it is a tradeoff the industry has to confront honestly.
What Has Been Recovered
STOLEN BYBIT FUNDS: STATUS AS OF APRIL 2025
Source: Bybit CEO Ben Zhou, public update April 2025
The Lazarus Bounty program, which offered 10% of recovered funds as rewards, received over 5,400 bounty reports in its first two months. Only 70 were deemed valid. Zhou publicly called for more bounty hunters skilled at decoding mixer transactions.
One year after the hack, the picture is clearer but not encouraging. Elliptic's February 2026 retrospective confirmed that the vast majority of stolen Bybit funds have now been fully processed through the laundering pipeline. The practical window for meaningful recovery has closed for most of the stolen amount.
For context, this follows historical precedent. When the same group stole $600 million from the Ronin Network (Axie Infinity) in 2022, only $30 million was ever recovered despite significant law enforcement involvement. That $30 million recovery rate, roughly 5%, is probably the realistic ceiling for state-sponsored crypto theft at this scale.
What the Bybit Hack Changed
Market impact. Ethereum dropped 24% and Bitcoin fell below $90,000 in the days following the breach. While broader macroeconomic factors contributed to the downturn, the hack intensified selling pressure and pushed the Crypto Fear and Greed Index into "extreme fear" territory.
Industry response. Bybit implemented over 50 security upgrades and completed nine third-party audits. Liquidity on the platform recovered to pre-hack levels within 30 days, according to analytics firm Kaiko. Somewhat counterintuitively, the exchange's user base grew from 50 million to 80 million registered users by year-end 2025, suggesting that transparent crisis management can actually build trust.
Regulatory acceleration. The EU and UAE moved to impose stricter KYC/AML requirements for exchanges. In the US, the incident fueled debate about balancing the new administration's pro-crypto stance with the security realities of state-sponsored theft at this scale. Discussions around mandating security audits and requiring transparency for crypto mixing services intensified across multiple jurisdictions.
The DPRK threat is growing. North Korea-linked actors stole over $2 billion in cryptocurrency during 2025, with the Bybit hack accounting for roughly 75% of that total. According to Chainalysis, cumulative DPRK crypto theft now exceeds $6 billion since 2017, with the proceeds reportedly funding the country's nuclear and ballistic missile programs. Elliptic's February 2026 analysis found that early 2026 exploit activity is running at roughly double the pace of the same period in 2025. A single nation-state has turned crypto theft into a funding mechanism for weapons development. That is not a hypothetical risk scenario. It is an ongoing operation with documented results.
The Core Lesson
The Bybit hack did not expose a flaw in blockchain technology. It exposed a flaw in how the industry manages the human and software layers built on top of it. The cryptography worked. The multisig worked. The interface that people trusted to tell them what they were signing did not.
What This Means for You
If you hold crypto on an exchange, the Bybit hack is not a reason to panic. It is a reason to think more carefully about where and how your assets are stored.
Does your exchange publish proof-of-reserves audits? Bybit had one completed within 72 hours of the breach. Not all exchanges commit to this level of transparency. If yours does not, that should factor into your risk assessment.
What custody tools does your exchange use, and who provides them? The Bybit hack was a third-party software compromise. Understanding who provides your exchange's wallet infrastructure, and how that infrastructure is secured, matters more than most people realize.
Do you keep all your holdings in one place? The basic principle of not storing everything on a single platform applies with even more force after an incident like this. For long-term holdings, self-custody through a hardware wallet removes exchange risk entirely, though it introduces its own responsibilities around seed phrase management and device security. Blockready's Module 6 (Wallets) and Module 13 (Research and DYOR) walk through both the exchange custody model and the self-custody model in detail, including the specific tradeoffs each approach creates and how to evaluate which one fits your situation.
Are you relying on labels or on understanding? "Cold storage" and "multisig" sound reassuring. But as Bybit demonstrated, those labels describe tools, not guarantees. The actual security depends on implementation, third-party dependencies, and the humans in the loop. Understanding how these systems work is the real protection, and it is exactly the kind of knowledge gap that leads to costly mistakes.
The Bybit hack will likely remain the defining security event of this market cycle. Whether the industry and individual holders learn from what it revealed is still an open question.
Frequently Asked Questions
Build the Knowledge That Prevents the Mistakes
Security in crypto starts with understanding how the technology actually works. Blockready's structured masterclass covers wallet security, exchange mechanics, and risk assessment across 13 modules and 150+ lessons. No hype. No shortcuts.
Explore Blockready